RISC-V: Reigniting innovation in semiconductors?
November 18, 2016

Do you remember when one advantage of the ARM architecture was its limited number of instructions? After all, the "R" in "ARM" stands for reduced inst...
Do you remember when one advantage of the ARM architecture was its limited number of instructions? After all, the “R” in “ARM” stands for reduced instruction set computing (RISC), and the benefit of this smaller instruction set architecture (ISA) was that it was simpler to program than complex instruction set computing (CISC) ISAs such as the x86-64 instruction set (which currently includes more than 2,000 instructions[1]). The more intuitive approach to programming and the fact that instruction sets for all ARM CPUs up to version 2 were available in the public domain helped the architecture gain popularity, and eventually aided in the mass adoption of ARM-based processors seen in the market today.
However, as ARM IP took hold in segments ranging from mobile to networking to embedded systems, it became necessary to develop new cores tailored to those applications (Cortex-A, Cortex-M, and Cortex-R variants among them), and with them, new instructions. As a result, an ISA that originally included fewer than 100 instructions ballooned to 1070 in the ARMv8 architecture according to researchers at the University of California, Berkeley, and ARM eventually elected to make their instruction sets proprietary in order to maintain them in accordance with their burgeoning semiconductor IP business. Unfortunately, the upfront licensing fees for an ARM IP core can range anywhere between $1 million and $10 million depending on the design[2], making the microarchitectures, and hence, the ISA, impractical for consideration by many academics and small startups.
Realizing the complexity of the Intel ISA and the exclusivity (and explosion) in ARM’s, a team of academics at the University of California, Berkeley embarked on a what they thought would be a short project to develop a new RISC-based ISA. After completing the ISA in 2010 they made it available to the open source community, but received several complaints when attempting to make a change to it shortly thereafter. At that point the team realized the opportunity for an open-standard RISC ISA that was locked down – indefinitely. And so, RISC-V was born.
Fewer and freer
RISC-V is an open standard ISA, but as opposed to other open-source RISC implementations like OpenRISC, it is not standardized around a particular processor microarchitecture. Rather, RISC-V defines four base integer ISAs for 32-, 64-, and 128-bit processors that contain fewer than 50 hardware instructions each: the 32-bit RV32I; the 64-bit RV64I; the 128-bit RV128I; and the RV32E, which is a 16-register subset of the RV32I.
A number of standard extensions also exist, including the general-purpose ISA (classified extension “G”); integer multiply/divide (classified extension “M”); atomic memory operations (AMOs) and load-reserved/store conditional (LR/SC, classified extension “A”); single-precision floating-point (classified extension “F”); double-precision floating-point (classified extension “D”); quad-precision floating-point (classified extension Q); and an optional compact subset for reduced code sizes (classified extension “C”). In addition, vector and crypto extensions are currently underway in working groups at the RISC-V Foundation.
RISC-V was designed to operate independently of microarchitectural features, and, as mentioned, once work on an ISA component is finished by the Foundation it is frozen, forever. The ISA also provides clear separation between system software layers, with straightforward communications between an operating system (OS) and the system or applications facilitated through a system binary interface (SBI) and application binary interface (ABI), respectively (Figure 1).
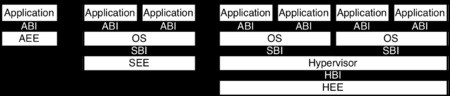
[Figure 1 | The RISC-V ISA communicates with the system execution environment (SEE) through a system binary interface (SBI), with the application execution environment (AEE) through the application binary interface (ABI), and with the hypervisor execution environment (HEE) through a hypervisor binary interface (HBI) in systems that employ a hypervisor.]
What this means for chip makers is that, outside of the locked down opcode space reserved for the base ISAs and extensions (both current and planned), the Foundation has guaranteed not to intrude on remaining greenfield opcode space with future modifications. That greenfield opcode space is therefore available for developers to create their own instructions, allowing the standard to be extended in a proprietary way that, as Ted Speers, Head of Product Architecture and Planning for the SoC Group at Microsemi and a member of the Board of Directors at the RISC-V Foundation reveals, allows them to innovate around the “secret sauce that is really in the microarchitecture that you build around it.”
“What’s important about the ISA at the end of the day is it’s not important. What’s important is that people can build and innovate a computer architecture with something that is well done,” Speers says. “Ultimately, the goal is that RISC-V becomes the common language of all new computer architectures going forward.
“Although at its root it’s just another ISA, a lot of thought has gone into making RISC-V extensible, so there are natural groupings of instructions that you might want to use,” he continues. “For a microcontroller (MCU) you might just want to use the compressed instructions, or not the floating-point instructions. The point there is that the language is built and architected with different extensions that are appropriate for your application.”
The minimalist flexibility and technology agnosticism of the RISC-V ISA makes it applicable in processor designs ranging from embedded MCUs to high-performance data center processors, as well as in heterogeneous system on chips (SoCs) that include multiple IP cores (Figure 2). Traditionally, the various IP in complex SoCs has required vast amounts of expertise spread out over large teams just to get the assorted cores talking to one another, much of which can be eliminated through comprehensive RISC-V libraries, such as those being developed by NVIDIA.

[Figure 2 | The Microsemi SmartFusion2 SoC FPGA is among the first embedded processing solutions compatible with the RISC-V ISA (RV32IM implementation), and is supported by the company’s Libero SoC Design Suite and Eclipse-based SoftConsole integrated development environment (IDE).]
Equally as important as the technology is the fact that RISC-V is license- and royalty-free, and operates under a BSD open source license, not a GNU license. Under a BSD license the standard can be used and extended without having to return those proprietary extensions to the open source community, enabling companies to leverage the foundations of RISC-V while still protecting the differentiation of special instructions tied to a microarchitecture that set their solutions apart.
“If you’re in college or you’re at a startup and you want to make an innovation in computer architecture, your starting point should be RISC-V,” Speers says. “With RISC-V you can have complete control over the architecture you want to build with a well-designed ISA.”
Reigniting innovation in semiconductors
Tech industry giants such as Micosoft, HP, and Google have joined the RISC-V Foundation, alongside startups like Codasip and SiFive that are already bringing RISC-V-based solutions to market. RISC-V has been upstreamed by major open source projects including the Free Software Foundation, BeanUtils, the GCC, and Fedora, all of which indicates not only a growing amount of interest in RISC-V as an accessible technology, but also one with real commercial viability.
But it’s just another ISA, right?
“The whole vision is how to drive down costs, everywhere actually, starting with the ISA,” Speers explains. “I view RISC-V as the kernel for reshaping how design is done in semiconductors, and starting to dramatically lower the cost of producing new chips. That’s the end goal in mind. It’s not that the RISC-V Foundation can proudly say that they have this ISA, it’s that they want to dramatically lower costs – reignite innovation in semiconductors.”
To learn more about RISC-V, the RISC-V Foundation, or upcoming workshops, visit riscv.org.
References:
1. “How Many X86-64 Instructions Are There Anyway?” Accessed November 18, 2016. http://www.tuicool.com/articles/JJzAj23.
2. Shimpi, Anand Lal. “The ARM Diaries, Part 1: How ARM’s Business Model Works.” RSS. Accessed November 18, 2016. http://www.anandtech.com/show/7112/the-arm-diaries-part-1-how-arms-business-model-works/2.




