V2X technology makes cars safer
April 10, 2015

The software needed to operate a sophisticated new car can contain upwards of a hundred million lines of code - fifteen times more than the new Boeing...
The software needed to operate a sophisticated new car can contain upwards of a hundred million lines of code – fifteen times more than the new Boeing 787 Dreamliner – spread among dozens of processors, making it a very attractive target for hackers. Balancing the convenience features of a connected car with the reality of new security vulnerabilities is the biggest challenge facing the industry.
While automakers are struggling with ways to protect their new and existing connected cars, there’s a pair of technologies that were designed to be private and secure from the very start. These are the short-range wireless-based vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I) systems. The primary objective behind V2V and V2I (collectively referred to as vehicle-to-everything, or V2X, is to prevent accidents and save lives.
We need these technologies because during just one year in the United States, we drive over 3 trillion miles per year, we have over 6 million accidents, we lose 35,000 people, and we suffer more than 3 million injuries.
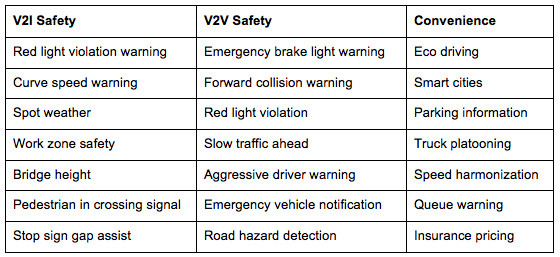
What can we expect from these technologies? The U.S. Department of Transportation has estimated that V2X can prevent 80 percent of accidents for unimpaired drivers by alerting them to the hidden dangers that can’t be sensed by traditional on-board equipment. By sharing data from any V2X-equipped vehicle within a half-mile radius, the driver can be alerted to the most common causes of accidents in time to take evasive action. The table shows some connected-car use cases.
V2X communications shouldn’t be confused with self-driving vehicles. The system has been designed to provide drivers with additional safety and convenience notifications that will be integrated with information from the many other on-board sensors. It’s still up to the driver, obviously, to drive the car. However, V2X is an enabling technology that one day will make even self-driving cars much safer by helping them see and react to invisible danger.
It was clear from Day 1 that V2X would not be accepted if drivers didn’t trust it. And if not accepted, the benefits will simply disappear. This is why two primary design requirements have been security and privacy. The system has been designed to ensure that every message shared between vehicles is certified as legitimate while removing ways to identify a driver or track a specific car. The system has also been designed to ignore messages from cars with compromised or poorly calibrated on-board equipment.
A number of challenges need to be overcome before we can all enjoy the benefits of V2X. For example:
- The technology adds about $250 to the cost of a car, although this will go down in the future
- We need a critical mass of V2X-equipped vehicles on the roads before the benefits begin to show
- Even though the U.S. Government will likely mandate inclusion of V2X for all cars built after 2019, under 10 percent of vehicles on the road are less than a year old and the aftermarket for V2X devices hasn’t started to be developed
- The secure credential management system (SCMS) needed to ensure the authenticity, security, and privacy of V2X communications has yet to be implemented
For the past two years, Gene Carter has been the Director of Product Management for the Embedded Security Business Unit at Security Innovation. Carter has spent the past 20 years in embedded and automotive product management roles for NXP Semiconductors, Philips Semiconductors, and Coto Technology. He holds an MBA from the University of Southern California’s Marshall School of Business and a BSc in Electrical Engineering from Tufts University.